How would you connect from your local machine to the database instance on the DBaaS server by using SQL*Net?
- A. You start an SSH process on your local machine to communicate to a tunnel created onthe DBaaS server.
- B. You must use port 1521 and the TCPS communication protocol.
- C. You can use only the SSH connection that is defined on port 22 that is configured by default during DBaaS instance installation.
- D. You must use Transparent Data Encryption(TDE) to secure connections to the DBaaS database instance when using SQL*Net connections from your local machine to DBaaS database instances.
Answer : B
Explanation:
To confirm remote access to the database through the SQL*Net security rule, create a connection to the database in Oracle SQL Developer. When creating the connection, fill out the fields as follows:
After entering values, click Test to test the connection.
Note: TCPS is TCP/IP with SSL.
References: Using Oracle Database Cloud Service (February 2017), 4-24 https://docs.oracle.com/en/cloud/paas/database-dbaas-cloud/csdbi/using-oracle-database- cloud-service.pdf
You want to make sure that Oracle Application Express (APEX) is enabled and accessible.
Which two steps must you perform?
- A. Unblock the APEX instance’s VM and follow the URL toinstance-ip-address:4848.
- B. Enable APEX in the Oracle GlassFish Server Administration Console.
- C. Create an SSH tunnel to port 443 on the instance’s VM.
- D. Selectdeploy_enablefrom the DBaaS instance monitor.
- E. Selectapex_launchfrom the GlassFish Server Administration Console monitor.
Answer : A,C
Explanation:
To access the administration console when the HTTPS port is unblocked:
References:https://docs.oracle.com/en/cloud/paas/database-dbaas-cloud/csdbi/access- apex-admin-console.html
Which two tasks can you perform on the Database Cloud Service Instance View page?
- A. You can add pluggable databases (PDBs) to thedatabase.
- B. You can decrease the storage of an instance.
- C. You can see patching information.
- D. You can create new users to access an instance.
- E. You can scale up to increase the shape of the current instance.
Answer : C,D
Explanation:
References:https://docs.oracle.com/en/cloud/paas/database-dbaas-cloud/csdbi/service- console-services-page.html
You want to perform database recovery with the most recent backup.
Which command would you execute?
- A. dbaascli rec –args –latest
- B. dbaascli orec –args-latest
- C. dbaascli rec –args -last
- D. dbaascli orec –args -last
Answer : B
Explanation:
dbaascliorec latest command restores the most recent backup and performs complete recovery.
References:https://docs.oracle.com/en/cloud/paas/database-dbaas- cloud/csdbi/dbaascli.html
Which two statements are true about Database as a Service (DBaaS) or about Database
Schema Service in Oracle Public Cloud?
- A. With Database Schema Service, there is a separate database for each schema.
- B. With DBaaS, you get a dedicated database instance or instances.
- C. With Database Schema Service, the schema or schemas may be in the same database as other schemas that belong to other subscribers.
- D. With DBaaS, you cannot decide when to patch the database home.
- E. With Database Schema Service, the schema may be in an Oracle Database 12c pluggable.
Answer : B,C
Explanation:
Database Schema Service uses schema isolation to implement multi-tenancy, which allows full transparency while still providing efficient use of database resources. The Oracle
Database is, at its core, a multiuser system for sharing data, so Database Schema Service simply uses the capabilities built up for the Oracle Database to share resources among multiple Database Schema Service customers.
What are two things can you do on the My Services Dashboard page?
- A. You can customize the metric icon for eachvalid service.
- B. You can add a data center and identity domain to your Cloud account.
- C. You can activate services for the current data center and identity domain.
- D. You can check the overall status of your active services for the current data centerand identity domain.
Answer : C,D
Explanation:
TheMy ServicesDashboard shows information limited to one identity domain in your account.
References: Using Oracle Database Cloud Service (February 2017), page 8-26 https://docs.oracle.com/en/cloud/paas/database-dbaas-cloud/csdbi/using-oracle-database- cloud-service.pdf
Which two problems indicate that you should consider scaling up your Database as a
Service (DBaaS) instance that hosts an Oracle Database 12c multitenant container database (CDB) with four pluggable databases (PDBs)?
- A. shortage of CPU for two PDBs in the CDB
- B. shortage of I/O bandwidth for the parallel queries that are issued by the CDB instance
- C. shortage of memory for the DBaaS instance
- D. shortage of memory in the Shared Pool of the CDB
- E. shortage of CPU for the DBaaS instance
Answer : C,E
Explanation:
References:https://docs.oracle.com/cloud-machine/latest/dbcs_dbaas/CSDBI/GUID-
457D283C-D890-4B4F-B65C-26D05B4C80CC.htm#CSDBI3339
You are using access rules to control network traffic among your DBaaS instances.
Which statement is true about access rules?
- A. They are used only for configuring external server access to DBaaS and do not impact how network groups communicate.
- B. They define a specific communication path, which consists of a source, destination, and protocol-port combination overwhich communication is allowed.
- C. They are used to map an external user to a database user to allow the user to communicate with and access the database.
- D. They are used to encrypt communication between DBaaS instances.
Answer : B
Explanation:
On the Access Rule youcan define the following:
References:https://docs.oracle.com/en/cloud/paas/database-dbaas-cloud/csdbi/service- console-access-rules-page.html
You want to make sure that your database administrators have a convenient way to monitor your DBaaS instance. To do so, you need to enable the Oracle DBaaS Monitor.
How would you enable the Oracle DBaaS Monitor?
- A. Use theenable_dbaas_monitorcommand.
- B. Create an SSH tunnel to port 443.
- C. Disable theora_p2_httpsslsecurity rule in Oracle Compute Cloud Service Console.
- D. Use the Oracle GlassFish Server Administration Console.
- E. Add ODBM access to each DBA’s user profile.
Answer : B
Explanation:
To access Oracle DBaaS Monitor when the HTTPS port is blocked, you must create an
SSH tunnel to port 443 on the compute node hosting the DBaaS Monitor.
Note:How you access Oracle DBaaS Monitor depends on whether the HTTPS port (443) hasbeen unblocked. When a Database Cloud Service deployment is first created, theHTTPS port is blocked to ensure network security
With Oracle Database Cloud Service as the subscription type, you must configure a database for Backup and Recovery.
Which two options do you have to back up your database instance?
- A. No backups required. You are responsible for configuring the database backups.
- B. Backup to cloud storage and VM block storage. Ten days worth of backups are kept, with five most recent days worth of backups available directly on VM block storage.
- C. Backup to Oracle Cloud Service storage volumes that is equal to five times the value that was provided in Usable Data Storage when the instance was created.
- D. Backup to cloud storage and VM block storage. Fourteen days worth of backups arekept, with seven most recent days worth of backups available directly on VM block storage.
Answer : A,C
Explanation:
When creating a new database deployment on Oracle Database Cloud Service, you choose whether you want automatic backups to be configured for the database. Your choices are:
Both Cloud Storage and Local Storage30 days' worth of backups are kept, with the 7 most recent days' worth available directly on the compute nodes local storage.
Cloud Storage Only30 days' worth of backups are kept, with all backupson cloud storage.
Noneautomatic backups are not configured.
References:https://docs.oracle.com/en/cloud/paas/database-dbaas-cloud/csdbi/db- deployments.html
The first step to connecting to Oracle Cloud is generating an SSH key pair.
To generate a key pair on a Unix or Linux machine, you would run the ssh-keygen utility.
What should be the number of bits in the key that must be created?
- A. 1014
- B. 2024
- C. 2048
- D. 1234
Answer : C
Explanation:
To generate an SSH key pair on UNIX and UNIX-like platforms using the ssh-keygenutility:
Etc.
References: Using Oracle Database Cloud Service (February 2017), page 3-3 https://docs.oracle.com/en/cloud/paas/database-dbaas-cloud/csdbi/using-oracle-database- cloud-service.pdf
You are working on a DBaaS database instance.
Identify the location for the associated database files for your instance.
- A. The installer sets the database file locations during installation by configuring the data file storage options.
- B. The DBaaS database instance data files are stored at:/u01:Oracle product software; the entire bits Compute Cloud storagevolume/u02:Oracle Database data storage; the entire data Compute Cloud storage volume/u03:Database backup storage; the entire fra Compute Cloud storage volume/u04:Database redo logs; the entire redo Compute Cloud storage volume
- C. All DBaaS databasefiles are stored at/u01/app/oracle/oradata.
- D. The database file locations are read fromutldbfiles.oraand users can update this file to set their own locations.
Answer : B
Explanation:
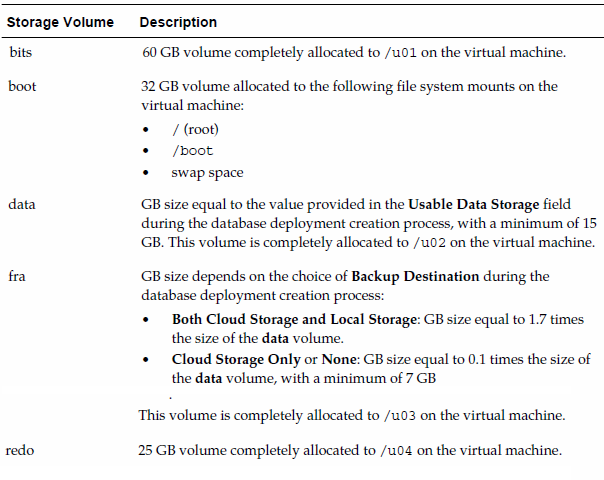
Compute Cloud Service Storage Volumes
When a Database Cloud Service databasedeployment is created at the Oracle
Database Cloud Service service level, the following storage volumes are created.
References: Using Oracle Database Cloud Service (February 2017), page A-9 http://docs.oracle.com/cloud/latest/dbcs_dbaas/CSDBI/CSDBI.pdf
Which two must be true when you migrate an Oracle Database 12.1.0.2 non-CDB to a database that is running in a Database as a Service (DBaaS) instance on Oracle Cloud by using the Remote Cloning method?
- A. The non-CDB may be opened in READ WRITE mode as long as ARCHIVELOG is enabled.
- B. The database link owner must have theCREATE PDBsystem privilege.
- C. The source platform must have the same endian format.
- D. The non-CDB must be in archivelog mode.
- E. The non-CDB must be opened in READ ONLY mode.
- F. The database link owner must have theCREATE PLUGGABLE DBsystem privilege.
Answer : E,F
Explanation:
To migrate an Oracle Database 12c non-CDB database to a Database Cloud
Service database deployment using the remote cloning method, you perform these tasks:
You can use this method only if the on-premises platform is little endian, the on-premises database release is 12.1.0.2 or higher, and the on-premises database and Database Cloud
Service database have compatible database character sets and national character sets.
References:https://docs.oracle.com/en/cloud/paas/database-dbaas-cloud/csdbi/mig- remote-cloning-non-cdb.html
Which two statements are true about the SSH tunnels within a Database as a Service
(DBaaS) Cloud environment?
- A. The SSH tunnel must be selected by an access rule to enable remote access.
- B. The server must hold the SSH public and private keys in the SSHauthorized_keysfile.
- C. DBaaS provides a centralized key server for all SSH connections.
- D. The client must provide the server with the SSH private key.
Answer : A,D
Explanation:
A: Oracle Database Cloud Service relies on Oracle Compute Cloud Service to provide secure network accessto database deployments. You can use the Oracle Database Cloud
Service console to perform network access operations such as enabling access to a port on a compute node, or creating new security rules.
D: Creating an SSH tunnel enables you to access a specific compute node port by using an
SSH connection as the transport mechanism. To create the tunnel, you must have the SSH private key file that matches the public key specified during the database deployment creation process.
References: Using Oracle Database Cloud Service (February 2017), 3-2 https://docs.oracle.com/en/cloud/paas/database-dbaas-cloud/csdbi/using-oracle-database- cloud-service.pdf
You are configuring network connections to your database instance.
What does each network group represent?
- A. It is used to allow unrestricted communication among some of your DBaaS instances byusing a set of defined policies and access rules.
- B. It is used to define load balancing and failover configurations between RAC database instances.
- C. It is used to define network connections to the Pluggable Databases (PDBs) within a Container Database.
- D. It is used to manage the connections between your external application servers (application servers that you currently use in your business environment) and your DBaaS instances.
Answer : A
Explanation:
Network groups provide a method for VMs to be grouped together forcommunications and firewall rules. You can define network groups to allow VMs within agroup to communicate with each other, while also preventing those VMs fromcommunicating outside the group.
Note:
Access rule. Access rules define the permitted paths of communication for VMs that are within a network group. You can define an access rule to enable a specific path of communication between two network groups, or between a network groupand a specified list of IP addresses.
References:http://www.oracle.com/webfolder/technetwork/tutorials/obe/cloud/dbaas/OU/Intr oDBaaS/ConfiguringNetworkSettings/ConfiguringNetworkSettings.html#section2s2

